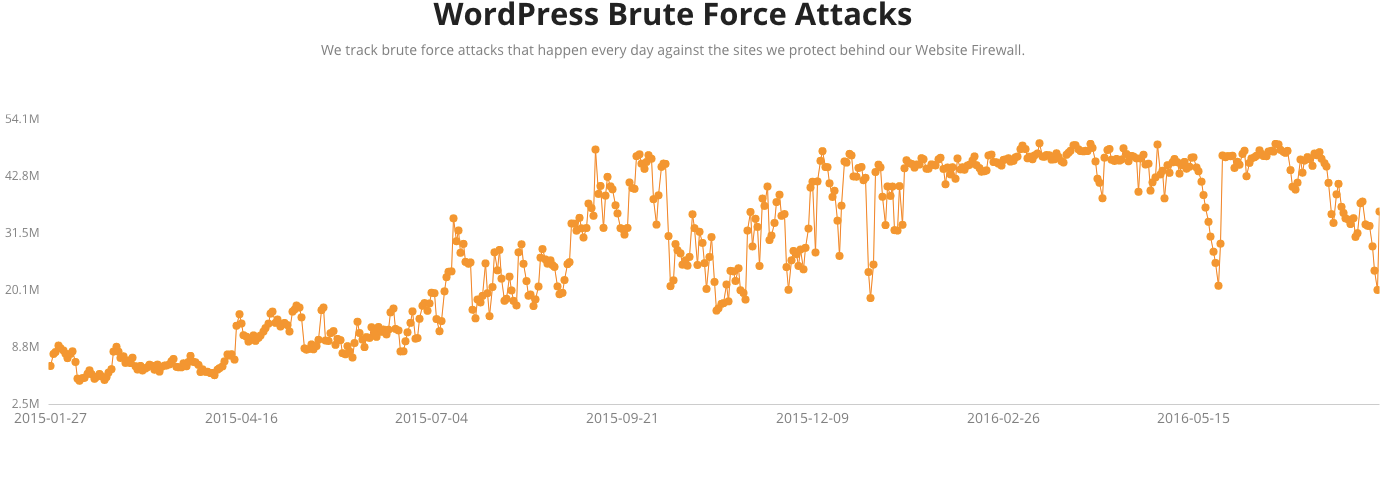
When it comes to improving the security of WordPress ecosystem one of the things that is desperately needed is better security information. For example, if you were to look at discussions of WordPress security you would likely to believe that there were a lot of attempts to brute force WordPress admin passwords, despite the evidence from the WordPress security companies claiming they are happening showing that those supposed brute force attacks are not happening at all. Unfortunately, one of the parties we have recently found being an impediment to improving security information that is available to the public is WordPress, or more specially, one or more of the people involved in moderating their forums.
Several weeks ago we discussed how someone at WordPress was disappearing some of our posts on the wordpress.org support forum and it has happened again just in the last day. Since one of the threads that had a reply of ours removed, touches on some important security issues that are in need better information, we thought it would be a good idea to discuss it here, especially since someone at WordPress doesn’t want accurate security information related to that to be accessible to people reading their forum for some reason.
One of the things we do to keep track of what plugin vulnerabilities are out there to make sure we provide the best data for our Plugin Vulnerabilities service is to monitor the wordpress.org support forums for threads discusses such issues. In doing that we run into threads discussing an assortment of other security issues, which we sometimes add a response when we can provide some insights based on knowledge of plugin security and hack cleanups of WordPresw website. Yesterday we ran into a thread involving a claim that several websites were hacked due to a third-party library included with WordPress, SWFUpload.
There we several things that stuck out to with this post. One, was that person, who discussing a hack of several of their clients websites, did not appear to have tried to properly determine how the website were hacked, instead they just seem to be guessing that it was caused by SWFUpload:
Now I think I found the hackers method, I believe they used “swfupload”.
Any security scan will not show “swfupload” as a danger because WordPress (foolishly) includes these script files for legacy reasons. Apart from that, the files in folder “swfupload” are not needed for current WordPress installs. These are old files and since they are old they are NO longer updated to stop hackers.
Now that I had 2 client websites hacked and malicious files uploaded, I believe that is the weak spot in WordPress allowing the hacker to gain access.
If that were the source of the hackings there should be evidence of the log files, which their post made no mention of reviewing (despite being a basic part of a hack cleanup). It seems highly unlikely that was the source, since if a hacker were to have discovered a vulnerability that allows hacking websites throughWordPress it is likely they would try to hack as many websites as possible quickly before it was discovered that their was issue since once it was, WordPress could quickly release an automatic update that would protect the vast majority of WordPress websites within a day. Seeing as we haven’t seen any evidence to point to a hack of WordPress itself occurring recently, it seem unlikely that was the source. The first two paragraphs (of total a three) of our response discussed those things:
If there was a known vulnerability that could be exploited like this in the version of SWFUpload included with WordPress it is likely that there would be a lot of websites being hacked through it right now, but we are not seeing any evidence of something like that going on at this point, so it isn’t likely to be the source of your hackings.
What you will want to do is to review the log files for the websites to see what evidence they provide as to the source of the hackings. If SWFUpload was in fact the source then there should be evidence of that in the HTTP log and that evidence would also provide information needed for the WordPress developers to work on fixing it.
The other major thing that stuck out what this person surprise that the website had been hacked while using the Wordfence Premium service:
I had 2 of my client WordPress sites hacked in this past month and they uploaded malicious PHP and JS files to infect the site with a backdoor PHP script. When I found the hacked upload 2 weeks ago in one client’s site, I wondered how did they got into the site while using WordFence Premium?
Should that be surprising? Not to anyone who is actually knowledgable about security, since in reality the various website security products and services out there provide at best limited protection against real threats against websites (and sometimes they actually are the security threat). For example, a WordPress security plugin would have no ability to stop an attacker who gains access to the FTP credentials from accessing the website’s files and in fact if the attacker wanted to they could modify the security plugin to ignore any changes they made to the website.
For Wordfence in particular it wasn’t surprising to us that their service wouldn’t protect a website considering among other thing they are one of the security companies pushing false claims of brute force attacks (while advertising that their service will protect you from them) and that we recently found their claim that their plugin would protect against stored XSS vulnerabilities was not supported when testing real world vulnerabilities against it. When it comes to their paid service, Wordfence Premium, back in June we noted that it was failing to detect vulnerabilities that were being exploited in the current versions of plugins. We concluded our response by mentioning that, since it is relevant for someone thinking that the service would protect them, that said service is oblivious to vulnerabilities that are being exploited and could actual be a cause of the hackings:
Since you brought up Wordfence Premium, it is worth noting that the service looks to have missed detecting exploitation of numerous vulnerabilities that were in the current version of WordPress plugins, so its ability to protect websites against real world threats is at least somewhat limited.
Was someone at WordPress trying to cover up the fact that Wordfence Premium has serious problem in its protection by removing our response, we don’t know, but removing our post had the same effect.